Strategic Threat Modeling
Build security into your DNA. Our architecture-first approach identifies design-level vulnerabilities before a single line of code is ever written.
Prevention is More Effective than Cure
Most security budgets are spent on reactive measures—patching bugs and monitoring for breaches. Threat Modeling flips the script by analyzing the blueprint of your system to identify architectural flaws that no amount of patching can fix.
Whether you're building a FinTech API or a cloud-native microservices architecture, ARM Innovations helps you visualize trust boundaries and data flows to preemptively define security requirements.
- Architecture Blueprint & DFD Analysis
- Business Logic Vulnerability Mapping
- Identification of Trust Boundaries
- Proactive Security Requirement Definition
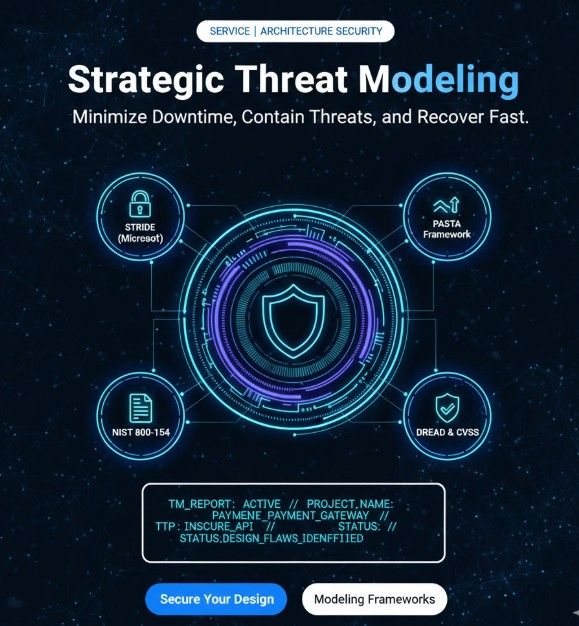
Global Modeling Frameworks
We use industry-standard methodologies to ensure every potential attack vector is analyzed and mitigated at the design phase.
STRIDE (Microsoft)
Systematic classification of threats: Spoofing, Tampering, Repudiation, Information Disclosure, DoS, and Elevation of Privilege.
PASTA Framework
Process for Attack Simulation and Threat Analysis – a risk-centric and business-aligned modeling methodology.
NIST 800-154
Data-centric threat modeling focused on how sensitive information flows through complex architectures.
DREAD & CVSS
Quantitative risk assessment to prioritize threats based on damage, reproducibility, and exploitability.
The Modeling Lifecycle
System Decomposition
Mapping the high-level architecture, trust boundaries, and identifying all entry/exit points for data.
Data Flow Mapping (DFD)
Visualizing how information travels between modules, databases, and third-party APIs.
Threat Identification
Applying STRIDE or PASTA to hypothesize every possible way an attacker could disrupt the system.
Countermeasure Definition
Defining technical controls (encryption, MFA, WAF) required to mitigate each identified threat.
Residual Risk Audit
Evaluating the system's security posture after controls are implemented to ensure safety.
Attack Vectors Identified
Architect for Resilience
Don't leave your system architecture to chance. Get a professional threat model report before you deploy.
