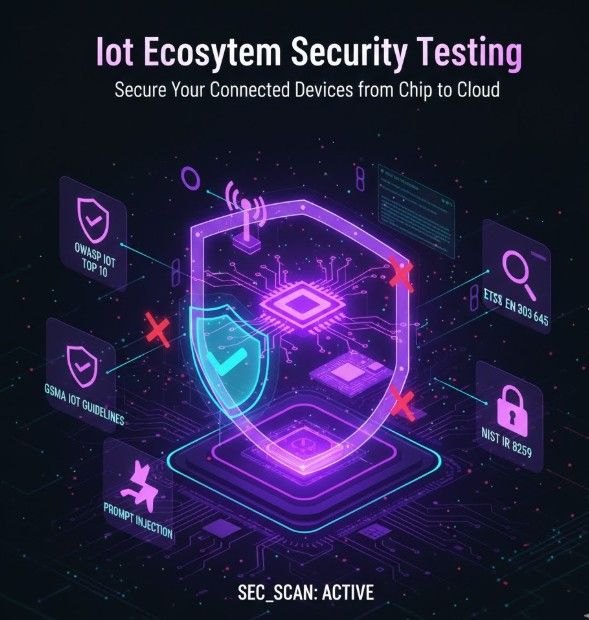
IoT Ecosystem Security Testing
Secure the entire chain of your connected devices. From hardware and firmware to mobile apps and cloud backends, we perform deep-dive audits to prevent unauthorized access.
Defense Across the Connected Fabric
Internet of Things (IoT) devices often introduce hidden entry points into otherwise secure enterprise networks. A single vulnerable smart camera or industrial sensor can become a bridge for attackers to pivot into sensitive production environments.
ARM Innovations provides specialized IoT security testing that goes beyond network scanning. Our experts perform chip-level debugging, firmware reverse engineering, and protocol analysis to find the flaws that automated tools miss.
- Physical Hardware & Component Audits
- Firmware Reverse Engineering & Binary Analysis
- Radio Protocol Testing (LoRaWAN, Zigbee, BLE)
- Cloud Backend & Mobile Integration Security
Global IoT Benchmarks
Our methodology is anchored in international standards to ensure your IoT deployment is resilient against emerging hardware and software threats.
OWASP IoT Top 10
Addressing critical risks like insecure web interfaces and weak passwords in IoT ecosystems.
GSMA IoT Guidelines
Following the GSMA's best practices for end-to-end IoT security architecture.
NIST IR 8259
Alignment with NIST recommendations for IoT device manufacturers and operators.
ETSI EN 303 645
Adherence to the European standard for consumer IoT cyber security.
End-to-End Audit Process
Device Recon & Mapping
Identifying physical interfaces (UART, JTAG), communication ports, and cloud associations.
Firmware Analysis
Extracting and reverse-engineering firmware to uncover hardcoded secrets and logic flaws.
Radio & Protocol Audit
Testing wireless protocols (BT/BLE, Zigbee, LoRaWAN, WiFi) for interception and replay attacks.
Cloud & App Assessment
Evaluating the security of the mobile companion apps and the cloud backend infrastructure.
Deep Exploitation
Performing hardware-level attacks and protocol manipulation to demonstrate actual risk.
Vulnerabilities We Uncover
Securing the Future of Connectivity
Don't let your IoT devices be the gateway for a network breach. Get an expert security audit today.
