Root Cause Analysis (RCA)
Don't just contain the breach—understand it. Our forensic experts perform deep-dive post-incident investigations to identify the 'Why' behind every security event.
Moving Beyond Surface Remediation
After an incident, organizations often rush to wipe systems and restore service. While containment is vital, failing to perform a proper Root Cause Analysis (RCA) almost guarantees a repeat of the breach.
ARM Innovations provides an independent, technical autopsy of your security incidents. We use advanced digital forensics to verify if a breach was a targeted attack, a result of unpatched systems, or a symptom of deeper architectural logic flaws.
- Adherence to Legal Chain of Custody
- Deep-Dive Registry & Memory Forensics
- Malware Capability Assessment
- Strategic Resilience Recommendations
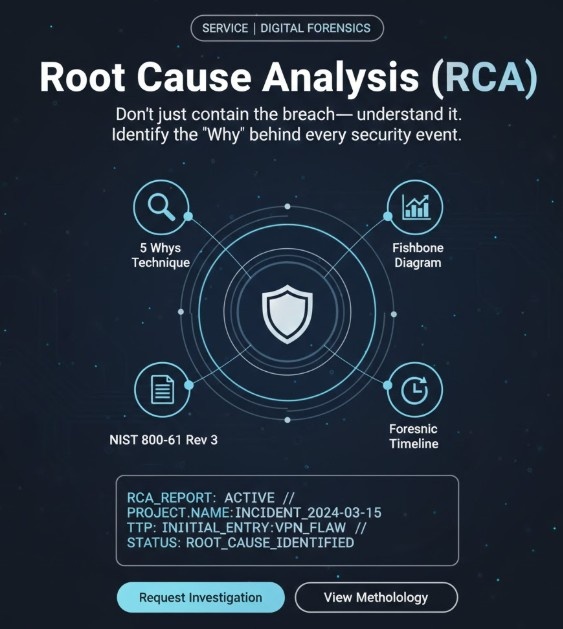
Scientific Investigation
We don't guess; we use evidence-based methodologies to prove how an incident occurred.
5 Whys Technique
Iterative interrogation to peel back layers of symptoms until the fundamental source of a breach is identified.
Fishbone Diagram
Visualizing causal factors across categories like People, Process, Technology, and Environment.
NIST 800-61 Rev 3
Following the latest federal guidelines for incident handling and post-incident analysis.
Forensic Timeline
Reconstructing a minute-by-minute sequence of events from logs, memory, and disk artifacts.
Investigation Lifecycle
Evidence Preservation
Ensuring all forensic artifacts (RAM dumps, firewall logs, EDR telemetry) are cryptographically hashed and secured.
Path of Infection
Identifying the 'Patient Zero' and the exact vector of initial entry into the corporate perimeter.
Lateral Movement Audit
Tracing how attackers moved through the network, which accounts were compromised, and what data was staged.
Causal Determination
Determining if the breach was due to a technical bug, configuration error, or human architectural oversight.
Strategic Hardening
Providing a long-term remediation roadmap to ensure the same attack vector can never be exploited again.
Forensic Artifacts Analyzed
Stop the Incident Loop Today
Identify the fundamental flaw and prevent the next breach before it even starts. Get a professional Root Cause Analysis report from our expert team.